How to Enable FTP Passive Mode
Last modified: 2026 February 27
Overview
This document explains how to use the active or passive mode to connect to a File Transfer Protocol (FTP) server.
The system enables passive ports 49152 through 65534 for Pure-FTPd servers and ProFTPD servers by default. If you use the ConfigServer Security & Firewall (CSF) firewall plugin, the system also adds passive port ranges to your server’s firewall by default.
If you use the nftables, firewalld, or iptables applications for your firewall, you must enable firewall settings for the passive ports manually. For more information about firewalls, read our How to Configure Your Firewall for cPanel & WHM Services documentation.
Active and passive mode sessions
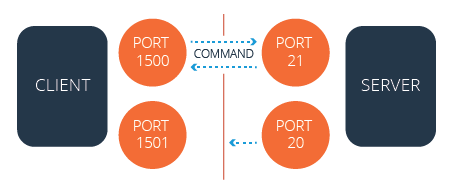
FTP uses a data port and a command port to transfer information between a client and a server. During a typical active mode session, the command port uses port 21 and the data port uses port 20. When you use a passive mode session, however, the data port does not always use port 20.
Active
In active mode, the FTP server responds to the connection attempt and returns a connection request from a different port to the FTP client. Network Address Translation (NAT) configurations block this connection request.
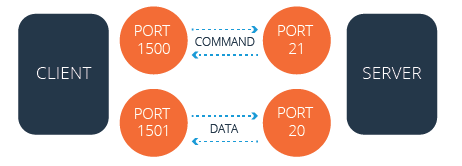
The firewall blocks the server’s attempt to communicate with the client because the server uses a different port than the first connection.
Passive
In passive mode, the FTP client initiates both connection attempts. NAT configurations do not block this connection request.
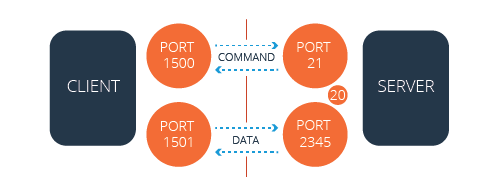
The firewall does not block the server’s attempt to communicate with the client because the client initiated the communication both times.
Configure FTP servers
The sections below explain how to edit the default configurations for a Pure-FTPd server and a ProFTPD server.
- A local file contains your desired settings which overwrite any default settings from the main file.
- The system enables passive ports
49152through65534for Pure-FTPd servers and ProFTPD servers by default.
Pure-FTPd servers
To edit the FTP configuration for a PureFTP server, perform the following steps:
- Log in to the server as the
rootuser via SSH. - Open the
/var/cpanel/conf/pureftpd/localfile, if it already exists, with a text editor. If it does not already exist, create the/var/cpanel/conf/pureftpd/localfile. - Add the desired changes to the file. If your FTP server exists behind a NAT configuration, set the
ForcePassiveIPoption to the FTP server’s public IP address, as in the following example:If your server does not exist in a NAT configuration, set the `ForcePassiveIP` option to the following entry:ForcePassiveIP: 203.0.113.0ForcePassiveIP: ~Important:Only oneForcePassiveIPentry can exist in a configuration file. - If you want to change your server’s default passive port range, run the following commands:
1 2echo "PassivePortRange: 49152 65534" >> /var/cpanel/conf/pureftpd/local /usr/local/cpanel/scripts/setupftpserver pure-ftpd --force - Configure your server to allow the passive port range to pass through the firewall. To do this, follow the directions in the Configure the firewall section below.
- Restart the PureFTP service with the following command:
/usr/local/cpanel/scripts/setupftpserver pure-ftpd --forceProFTPD servers
To edit the FTP configuration for a ProFTPD server, perform the following steps:
- Log in to the server as the
rootuser via SSH. - Open the
/var/cpanel/conf/proftpd/localfile, if it already exists, with a text editor. If it does not already exist, create the/var/cpanel/conf/proftpd/localfile. - Add the desired changes to the file. If your FTP server exists behind a NAT configuration, set the
MasqueradeAddressoption to the FTP server’s public IP address, as in the following example:If your server **does not** exist in a NAT configuration, set the `MasqueradeAddress` option to the following entry:MasqueradeAddress: 203.0.113.0MasqueradeAddress: ~Important:Only oneMasqueradeAddressentry can exist in a configuration file. - If you want to change your server’s default passive port range, run the following commands:
1 2echo "PassivePorts: 49152 65534" >> /var/cpanel/conf/proftpd/local /usr/local/cpanel/scripts/setupftpserver proftpd --force - Configure your server to allow the passive port range to pass through the firewall. To do this, follow the directions in the Configure the firewall section below.
- Restart the ProFTP service with the following command:
/usr/local/cpanel/scripts/setupftpserver proftpd --force
Configure the firewall
49152 through 65534 for Pure-FTPd servers and ProFTPD servers by default.
You may need to add your FTP server’s passive port range to the firewall manually.
ConfigServer Security & Firewall (CSF)
If you use the CSF plugin to manage your server’s firewall, open the /etc/csf/csf.conf file, and confirm that the passive port range exists at the end of the TCP_IN line. The system adds your FTP server’s passive port range to the firewall by default. For more information on how to use CSF, read CSF’s readme file.
- As of August 31, 2025, the developers of CSF no longer maintain or support it. They have released CSF under the GPLv3 license.
- On supported cPanel & WHM versions, WebPros International, LLC maintains its own version of CSF for security and stability updates only. We do not provide help with CSF configuration or troubleshooting. For more information, read our How to Install ConfigServer Security & Firewall (CSF) documentation.
- CSF does not function with the
firewalldutility. If you install CSF, you must remove thefirewalldutility. To do this, run theyum remove firewalldcommand.
nftables
If you use the nftables framework for your AlmaLinux OS, CloudLinux™ 8 or later, or Rocky Linux™ server, run the following commands to add the passive port range to your server’s firewall:
|
|
You will find the nftables ruleset for your server in the /etc/sysconfig/nftables.conf file.
firewalld
If you use the firewalld application for your CentOS 7, CloudLinux 7, or Red Hat® Enterprise Linux® (RHEL) 7 server, run the following commands to add the passive port range to your server’s firewall:
|
|
iptables
Red Hat Enterprise Linux (RHEL) 8 deprecated the iptables utility. While WebPros International, LLC does not support this version of RHEL, this change affects all cPanel-supported operating systems. We recommend the nftables utility for servers that run the AlmaLinux OS, Rocky Linux, or CloudLinux 8 or later operating systems. We recommend the firewalld utility for servers that run the CentOS 7, CloudLinux 7, or RHEL 7 operating systems. For more information, read Red Hat’s When to use firewalld, nftables, or iptables documentation.
If you use the iptables application for your FTP server’s firewall, perform the following steps to add the passive port range to your server’s firewall:
-
Install the
iptables-servicespackage if it does not already exist on your server. This package provides theiptablesandip6tablesservices, which are not included in theiptablesapplication. To install this package, run the following command:yum install iptables-services -
Run the following commands to add the rules to the firewall and save the configuration:
1 2iptables -I INPUT -p tcp --dport 49152:65534 -j ACCEPT service iptables save
SolusVM and Xen
If you use SolusVM and Xen® on a CloudLinux server, you may experience problems with Passive FTP. These problems may resemble a firewall or other connection issue, even when no firewall exists.
To resolve these issues, perform the following steps:
- Replace the
IPTABLES_MODULES=ip_conntrack_netbios_nsline in the/etc/sysconfig/iptables-configfile on the VPS node with the following line:IPTABLES_MODULES=ipt_REJECT ipt_tos ipt_TOS ipt_LOG ip_conntrack ipt_limit ipt_multiport iptable_filter iptable_mangle ipt_TCPMSS ipt_tcpmss ipt_ttl ipt_length ipt_state iptable_nat ip_nat_ftp ipt_owner ipt_REDIRECT - Run the
service iptables restartcommand to restart theiptablesservice.
Troubleshoot FTP passive mode
If your NAT-configured server cannot execute Passive FTP connections to other IP addresses on the server, set the ForcePassiveIP option with a tilde (~) character. The system interprets this character as an undefined directive and prevents automatic changes to the /etc/pure-ftpd.conf or /etc/proftpd.conf files.